
Data Security in the Age of Ransomware
In the current era of cyber insecurity and the associated everyday dangers impacting both global organizations and individuals, we see a significant effect on the economy in terms of financial loss, amounting to nearly trillions of dollars. We can also see, what has now become an almost every day encounter; security breaches and information leaks which have led to the exposure of sensitive business and end-user customer data.
The Threats
The risks are now proving very difficult to keep up with, and pose a significant threat even to those organizations that have technological resources. However, what is even more worrying is the billions of individuals who are using the Internet to service their everyday life needs. Individuals who have very little, or no understanding of the security threats and, most importantly, how to mitigate or recover from such adverse conditions. These risks vary in many forms. One very current example of a ransomware attack in 2020, which was crafted with the malicious intent of compromising a device to lockout the authorized user from their own data objects; or, locking out the entire system from user access is the Ransom EXX. Ransom EXX is known to have infected the headquarters of the Japanese company Konica Minolta with devastating effect. Ransom EXX is so new, as of today 8 August 2020 very little is known about this malware application – See Fig 1 below.
Fig 1 – Ransom EXX Knowledge Base
The threat posed by associated Advanced Evasion Techniques (AET) of ransomware attacks arrive in a profile which is developed to encourage recipients or end users through a precursor phishing message. Recipients are baited into clicking a malicious link(s) to invoke the activity of infecting the system – with the criminal usually offering to re-enable access with a ransom fee of around $350.
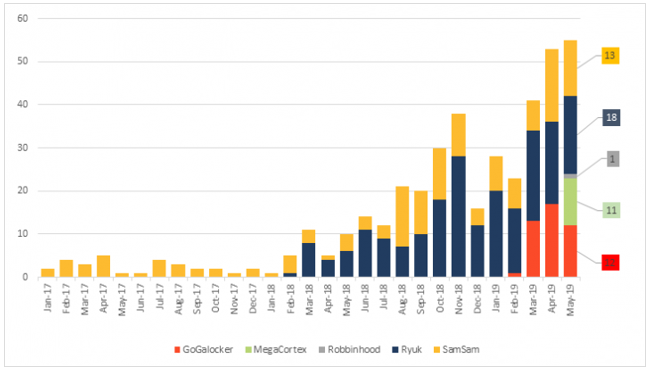
Fig 2 demonstrates the increased spread of popular Ransomware agents from January 2017, up to May 2019.
Fig 2 - Ransomware Growth 2017 - 2019
The Legal Position of Paying a Ransom
In research conducted into the holders of crypto-currency (the untraceable currency of the Ransomware Criminal Fraternity) it can be discovered that many large institutions have been known to keep a handy crypto-wallet as a backup resource, just in case they fall victim to a successful incursion. Big name companies have paid ransoms in hope that their data will be unlocked and restored. However, it is here where the grey line of legality may bring doubt, as when such payments are made, it not only breaches any active AML (Anti Money Laundering) policies, but can also lead to a criminal act where the paying organization may be directing funds into a criminal and potentially terrorist based organization.
This in turn can also breach CTF (Countering Terrorist Funding) – see reference [1] Financial Action Taskforce ‘Fighting Terrorist Financing’, which infers that giving into such demands provides terrorist organizations with the funds to support other criminal activities, ranging from the production of counterfeit goods through to people trafficking.
Big Picture First Hand Case Studies
To bring the subject of ransomware into alignment with a real-world hands-on operational encounter, we can focus on a case study which relates to the impact of a ransomware attack on a well-known UK company located within the hospitality sector. The first indications of the presence of a ransomware agent being resident on a server was detected by a third-party SOC (Security Operations Centre) located in the US, who informed the client during each monthly service call that they were hosting what looked to be a viral agent. However, given that the organization was running without a senior, knowledgeable security lead, the incumbent junior interim security manager decided that it would be dealt with during routine maintenance, at a future date, when that server would be subject to an update, as the viral agent was passive and not causing any issues. Thus, the threat vector was allowed to remain passively active and resident on that particular machine.
The unfortunate impact was realized when a wandering mouse-click of an internal user found the ransomware agent, and with one click the adverse payload was invoked – a process which locked down 7 production servers, and one front-of-house system serving as a payment kiosk for hotel guest and hosting multiples of PCI-DSS transactions. However, the ransomware agent had a number of other adverse facets, and it was soon discovered that it was calling home and sending packets of data to an offshore IP address – possibly credit card transactional data. As more in depth analysis was conducted it soon became evident that the agent was smart, as it took steps to locate and disable any on-system anti-malware protective defense on the booking workstation! The overall impact was lost revenue, a 6-day clean-up operation, and the matter of reporting the breach under the PCI-DSS mandated processes, which was action never taken!
There are of course many other examples of successful ransomware attacks which have caused significant disruption beyond the technological impact. One example is the case of the Lincolnshire County Council in 2016, who were under the management of a Serco outsourcing contract. The council was reported to have received a ransom demand of £1m. In this case, the disruption caused to the authorities’ data, the councils sub-divisions was so adverse that they could not process accounts, pay invoices or service their schools with supplies. Needless to say, whilst the incident was played down, it did cause the authority to claw back funds from Serco as a fine for their blundering and mismanagement.
In the aforementioned case studies, the organizations were large, with technical resources at hand to recover the data from their last backups (where possible), interact with the clean-up operation, and to carry out post attack measures to secure the enterprise with new configurations and defensive application upgrades. It is here however, that those whose sensitive and business data assets are at the greatest risk of exposure are within the communities of the everyday end-user public, and of course the business domains of the SME. According to research carried out by RICOH [2], it was concluded that there are vast opportunities for the criminals, with 58% of UK based SME’s paying the ransom.
A second report [3] published by Knowbe64 reported that they had noticed the trend of attacks occurring at a rate of 1 every minute, implicating SME’s which accounted for 62% of Ransomware attacks. Given that the SME sector tends to not accommodate adequate resources in the form of a technical cyber-savvy security posture and support capabilities, they clearly represent a very low hanging fruit target for a cyber-criminal. Which is why to date, multiples of such smaller user targets have suffered the real consequences of data-lockout, most of which have had to pay a ransom to save their business from extinction due to denied access to their critical operational data.
Landscape of Exposure
Looking back over the last decade in which Ransomware attacks have become a crafted money spinner for organized cyber-criminals, the real vulnerable exposure points have been twofold:
- Lack of up-to-date backups
- Easy access to data assets
aking the first vulnerability into account, if organizations have maintained a life-cycle of current backup strategies, in the recovery phase they may then have an opportunity to revert back to the last current data image and restore it – following up with a complete restoration of the corrupted systems. But as has been exemplified in so many ransomware attacks, particularly in the cases of individuals and the SME Sector, such backups are not always available, leaving only one option of response to the loss of data, i.e. yielding to the ransom demands in hope that the compromised data may be unlocked.
The second option is to take a proactive step around data availability. Here in the proactive mode, the end user and SME may take action, not only in the form of backing up, but also by denying the opportunity of data corruption and compromise by securing the valuable data assets, in what may be considered, an untouchable state. With larger businesses, they do have many options in the form of enabled areas of protected storage such as SAN (Storage Attached Network) and NAS (Network Attacked Storage), but for the multiples of end users, and the SME Sector, this may be out of reach, challenging and cost prohibitive. So, for the individual, or small business users alike, there is a very necessary and urgent need to serve a proactive defense to secure their valued data assets.
Logical Chain Security
Whilst we may assert that the larger commercial, and cross sector organizations and institutions are able to strengthen their approach to mitigating the threat, and to maximise their defensive posture, there is a need to urgently consider how the most exposed and vulnerable surfaces of potential attack are accommodated with a sensible, affordable and realistic cyber defense strategy to secure the digital assets (data/information). Here we look at enhancing the security profile of the billions of Internet users, as well as those resident within the SME sector to mitigate and reduce the opportunities for ransomware agents to successfully execute a lockdown.
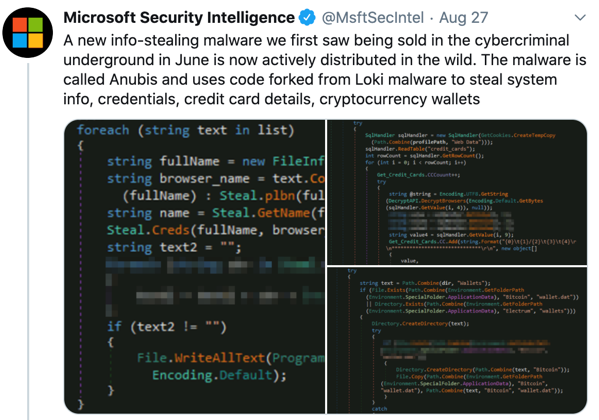
But it is not only ransomware which may implicate valuable end-user data objects. In August 2020, the Microsoft Security Intelligence Team reported on the Anubis Malware Agent which seeks out financial information assets, as well as those valuable cryptocurrency wallets that are open to access – a further reason why such valuable data assets should be stored off-line. See Fig 3 below relating to the Anubis [4] Malware Agent.
Fig 3 - Anubis Cryptocurrency Stealing Malware Agent
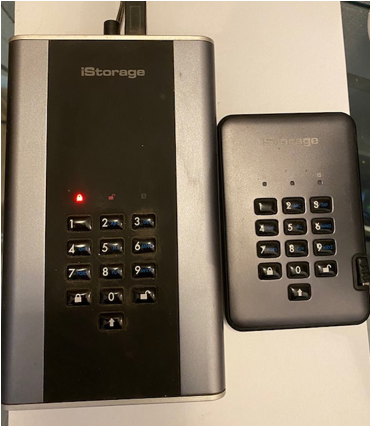
Given that the primary target is data, such valuable assets should be secured in a logical/ physical location. Thus, if a user does click on a link which invokes a ransomware process, the local system files or even the local computer may become unavailable, but the malicious agent cannot follow an active, available logical path to the main data objects. This simple, yet effective solution may be affordably facilitated with a secured drive with pin-access ACL (Access Control List) such as a diskAshur DT [5] (Desk Top) unit for the SME, and in the case of the everyday user a diskAshur Pro [6] will serve as an effective solution to protect their data. This will also allow for speedy recovery time and effort post attack - even if the drives are connected but not authenticated, the ransomware cannot gain access to the contents. Fig 4 is an example of the type of drives which may be used to secure data:
Fig 4 - Secured ACL Protected Encrypted Drives
The final stage of recovery would then be to reinstall the O/S which is not an arduous process for any user with moderate skills. In the event of failure, a visit to a PC Store will accommodate the recovery.
Conclusion
On the premise that cyber-insecurity is not going to go away anytime soon, with regular breaches of security leaking end-user data into the hands of criminals, we must consider the individual and the SME to be a target at mass. Additionally, due to the fact that such small users may be devoid of any expertise, one may conclude that on-mass set of targets they are subject to exploitation every single day. Solutions as suggested in this paper, may be considered by those with the technological security prowess to be simple. However, for those individuals and SME’s who use the Internet to conduct their everyday life and business practices, such simple solutions may be considered a business life saver.
If we are to start to put a dent in cyber-crime, we must place focus on the masses of end users and start to think small to mitigate the mass exposure of the vulnerable, forgotten public end-user.
References:
Ref [1] - Countering Terrorist Funding: https://www.fatf-gafi.org/media/fatf/content/images/TF-operational-reports-brochure.pdf
Ref [2] - RICOH Ransomware Report: https://insights.ricoh.co.uk/simplifying-technology/ransomware-attacks-are-successfully-targeting-small-to-medium-sized-businesses-how-do-you-protect-your-data
Ref [3] - Knowbe64 Ransomware Conclusions: https://blog.knowbe4.com/ransomware-incidents-increase-131-percent-with-the-smb-being-the-primary-target
Ref [4] - Anubis Malware Agent: https://latesthackingnews.com/2020/09/02/microsoft-warns-of-another-anubis-malware-targeting-windows/
Ref [5] - diskAshur DT: https://istorage-uk.com/product/diskashur-dt2/
Ref [6] - diskAsure Pro: https://istorage-uk.com/product/diskashur-pro2/
Related Articles

Keeping It Safe: How to Protect the Systems That Run Our Lives
Imagine a world where you wake up one morning to find your air-conditioning…

Value Creation with Artificial Intelligence
Our society creates petabytes of data, making predictions and improving…

What Can Pandemics Teach Us About Cyber Security?
We are living in a world in which we have either embraced technology,…

Resisting the Persistent Threat of Cyber Attacks
Delivering agile cyber-defense is now a must, with the recognition that…